Thoughts on Data Privacy
Harari reminds us that history is not deterministic. “The same technological breakthroughs can create very different kinds of societies”. Zuboff has highlighted an important phenomenon and provides a wakeup call to the academic, professional and political establishments. The field of Information Systems is well placed to illuminate the emerging field of commercial data surveillance as it transforms our society and influences our everyday actions. Smith et al. (2011)1 warn that the practice of commercial sharing of data by Facebook, Google and other major tech firms risks eventually alienating users. With increased awareness of the pervasiveness of surveillance capitalism, public opinion may shift and demand may emerge for products that better protect user’s privacy. For example, users may choose to pay for an encrypted email service such as ProtonMail rather than using Gmail. Noted venture capitalist Roger McNamee2 was instrumental in introducing surveillance capitalism into Facebook and is now vocal in his opposition to these practices and believes they will ultimately be self-destructive to the firm due to user backlash. Some scholars have illuminated other negative effects such as algorithmic discrimination, hidden political influence and the expansion of state influence on everyday lives34.
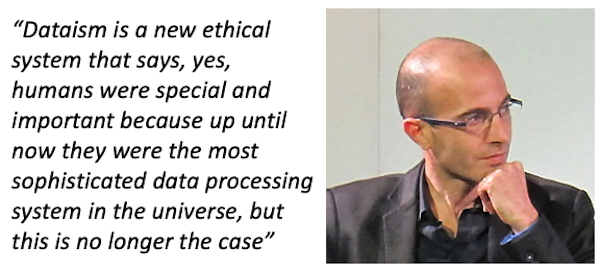
Yuval Noah Harari, 20165
This series of posts has focused on the more opaque aspects of surveillance capitalism, some of which could be interpreted as negative social developments. There are overwhelmingly positive aspects of recent technological progress in areas associated with data collection and open communication. Ubiquitous networking provides unprecedented access to educational opportunities and other knowledge based services and digital experiences that enhance everyday lives. New forms of consumer power have emerged that disrupt parasitic industry practices and deliver enhanced value to consumers. As discussed earlier, there are asymmetries of power at play. Facebook, Microsoft, Google and Amazon are at the forefront but there is little evidence they or other major players have abused this power imbalance beyond their corporate profit motives. These imbalances can be combatted through the use of accessible encryption and anonymization services. Should abuses occur on a significant scale then it is reasonable to assume that users would respond by employing some of these anti-surveillance techniques or by simply boycotting the offending services in favour of more secure modes of communication.
However, the concerns expressed in this series of blog posts about the secretive aspects of surveillance capitalism should not be dismissed as an overreaction or paranoia. Despite the rhetoric of transparent communications that the major players extol, they operate in a zealously guarded and secretive manner. The vast data centre infrastructure needed is only available to a select few. Algorithms used to collect data and influence users are purposefully hidden from view and treated as prized internal IP. The technology of surveillance capital is only available to the biggest handful of players.
Next: References
-
Smith, H.J., Dinev, T., Xu, H., 2011. Information Privacy Research: An Interdisciplinary Review. MIS Q. 35, 980-A27. ↩︎
-
McNamee, R., 2019. Zucked: Waking Up to the Facebook Catastrophe. Penguin Publishing Group. ↩︎
-
Crawford, K., Schultz, J., 2014. Big Data and Due Process: Toward a Framework to Redress Predictive Privacy Harms. Boston Coll. Law Rev. 93–128. ↩︎
-
Noble, S.U., 2018. Algorithms of Oppression: How Search Engines Reinforce Racism. NYU Press. ↩︎
-
Harari, Y.N., 2016. Homo Deus: A Brief History of Tomorrow. Harvill Secker. ↩︎
